At work, we have multiple brands and sites with different legal pages. The management decided to redirect all of these pages from multiple domains to point to a separate page on the main brand domain. It looks like this, legal.brand1.com will redirect to www.maindomain.com/brand1-legal, legal.brand2.com will redirect to www.maindomain.com/brand2-legal etc. While I was researching how to do this the easiest way, I’ve found some old articles that suggest using S3 buckets. This won’t work for me because it doesn’t support HTTPs. If you are looking to redirect HTTP traffic only, this is the way to go and you can skip this article. There is a workaround to use S3 and CloudFront, but this setup uses AWS issued certificates and I have my own. Finally, I’ve found an article that explains how to do this using an application load balancer in AWS. Here is a link to the article. I’ll expand a little bit more.
NOTE: Your sites doesn’t have to be hosted in AWS for the redirect to work. They can be hosted anywhere. Even in your basement. The only requirement is to have an ALB, SSL certificates and access to modify the DNS for the destination domain.
Here is my setup. I have 3 domains, all with valid HTTPS certificates and the destination domain DNS is in Cloudflare (the free version). We’ll redirect the following URLs as described below.
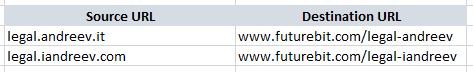
The redirection will work for both HTTP and HTTPS.
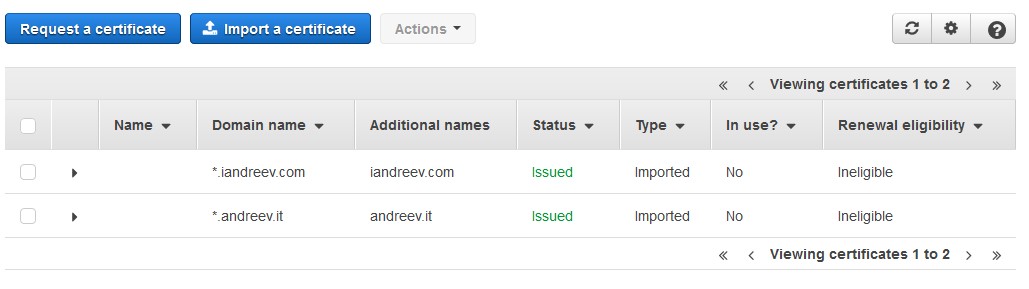
SSL certificates
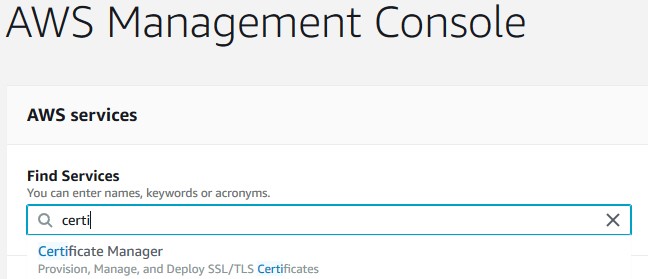
From the AWS console, open up the Certificate Manager.
Click on Get started under Provision certificates.
Click on Import a certificate from the top of the page.
Paste your certificate under the Certificate body which is your actual certificate in PEM format (usual extensions CER or CRT), then paste your private key (usual extension KEY) and the certificate chain (usual extensions CA or ca-bundle). The certificate chain is a combination of the CA certificate (the certificate of your certificate authority) and the intermediate certificate (you get these when you buy a certificate). Once completed click on Review and import.
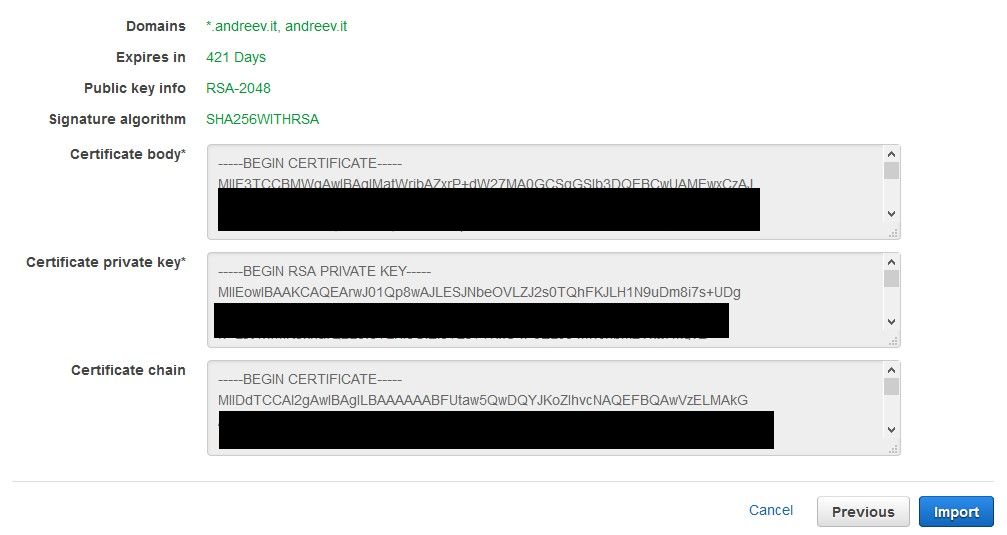
Click Import. Do this for the certificates for both source URL domains. You don’t have to install the certificate for the destination domain.
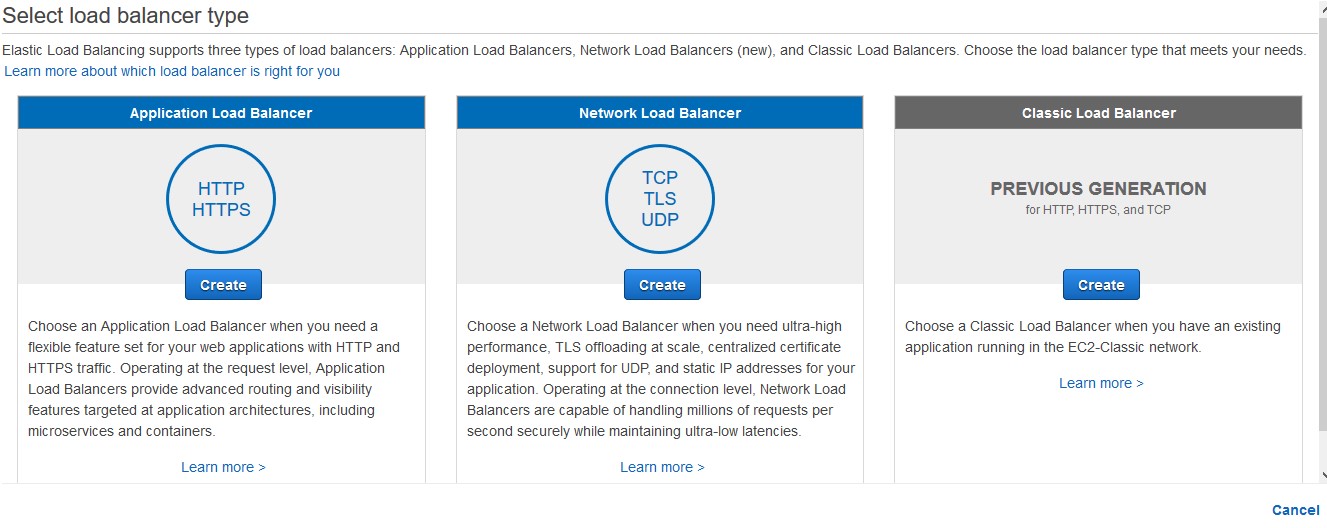
ALB (Application Load Balancer)
From the AWS console, go to EC2 service and then on the left side, look for Load Balancers. Click on Create Load Balancer and select Application Load Balancer.
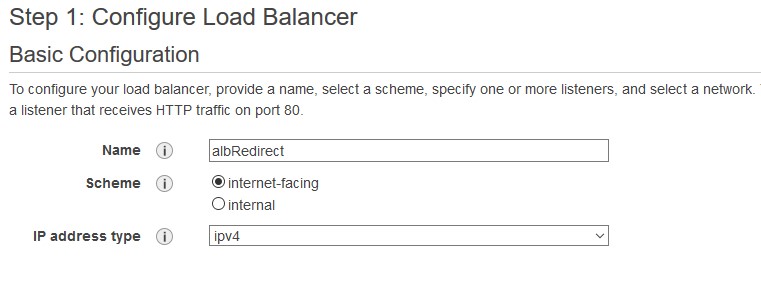
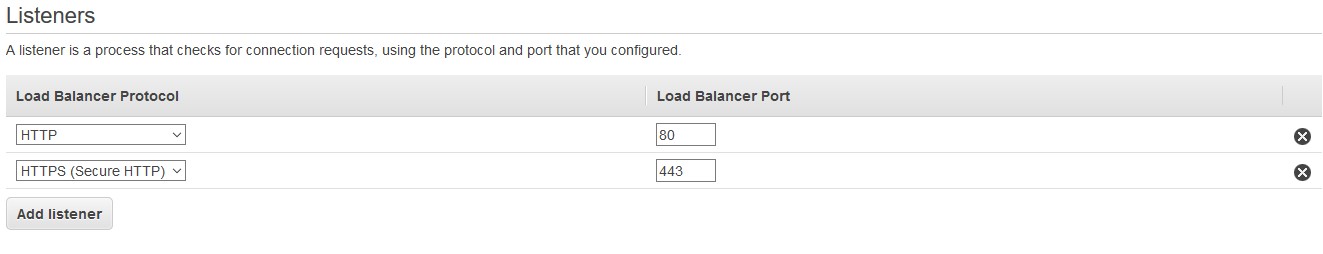
For step 1, name the load balancer (elbRedirect in my case), make sure it’s internet-facing and ipv4.
Click Add listener and add HTTPS.
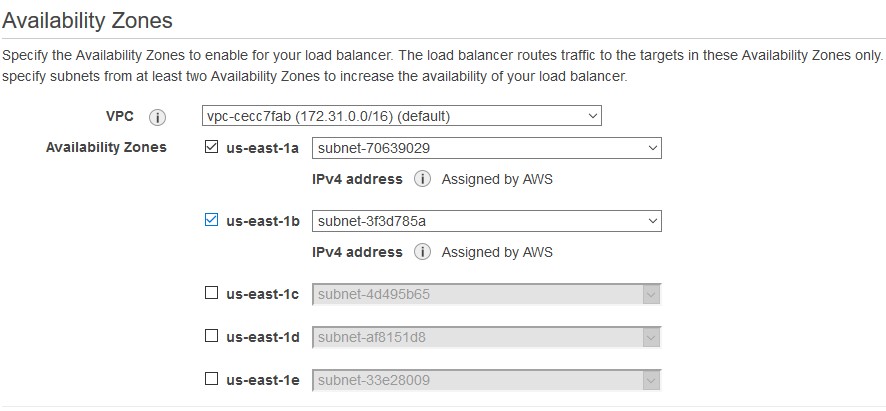
Choose at least two subnets. It really doesn’t matter what subnets you’ll choose even if your sites are hosted in AWS. We are using ALB as Layer 7 device, so the location is not important.
Click on Next: Configure Security Settings.
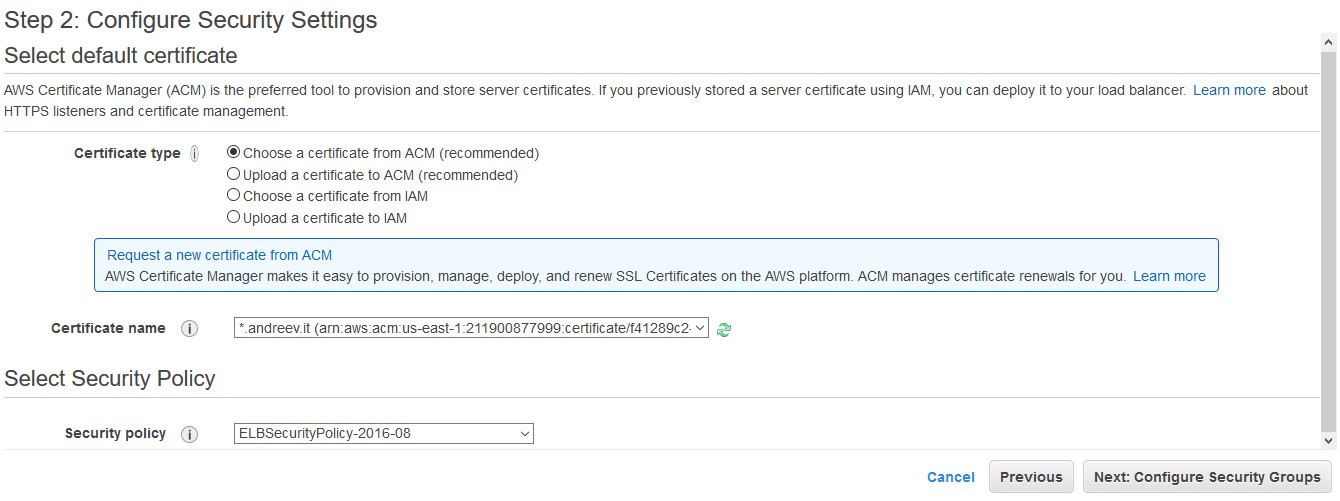
Choose a certificate for the domain that you want to redirect first. If you have only one certificate, choose that one.
Click on Next: Configure Security Groups.
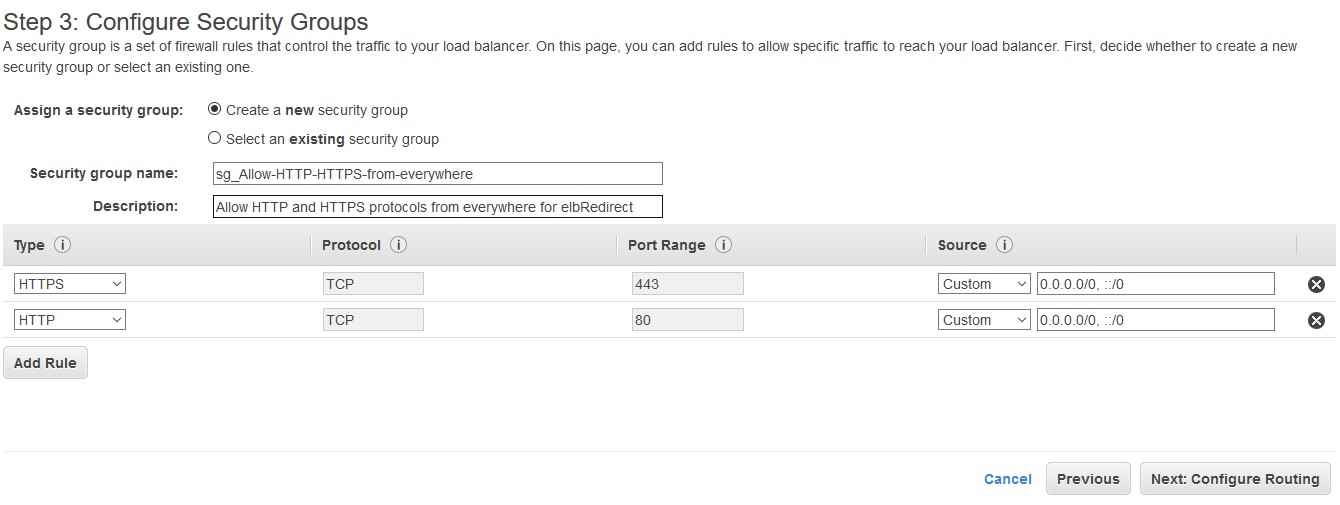
For step 3, select to Create a new security group, name it, add a description and add both HTTP and HTTPS from 0.0.0.0/0 (everywhere) as a rule.
Click on Next: Configure Routing.
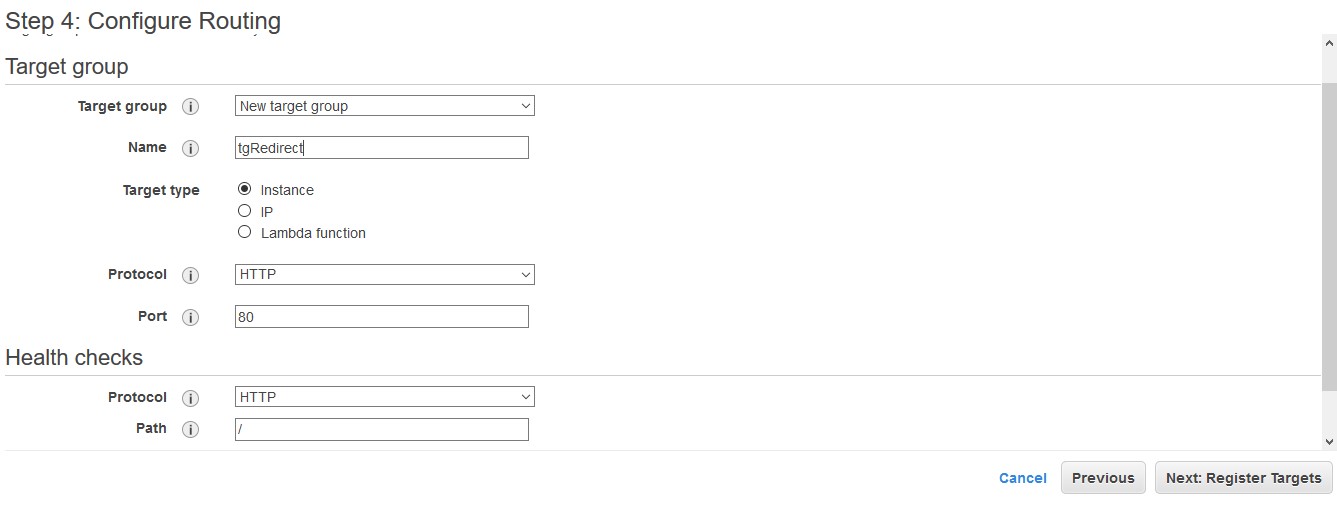
For step 4, select New target group and name it (tgRedirect in my case). You can leave everything else as-is. It’s not relevant.
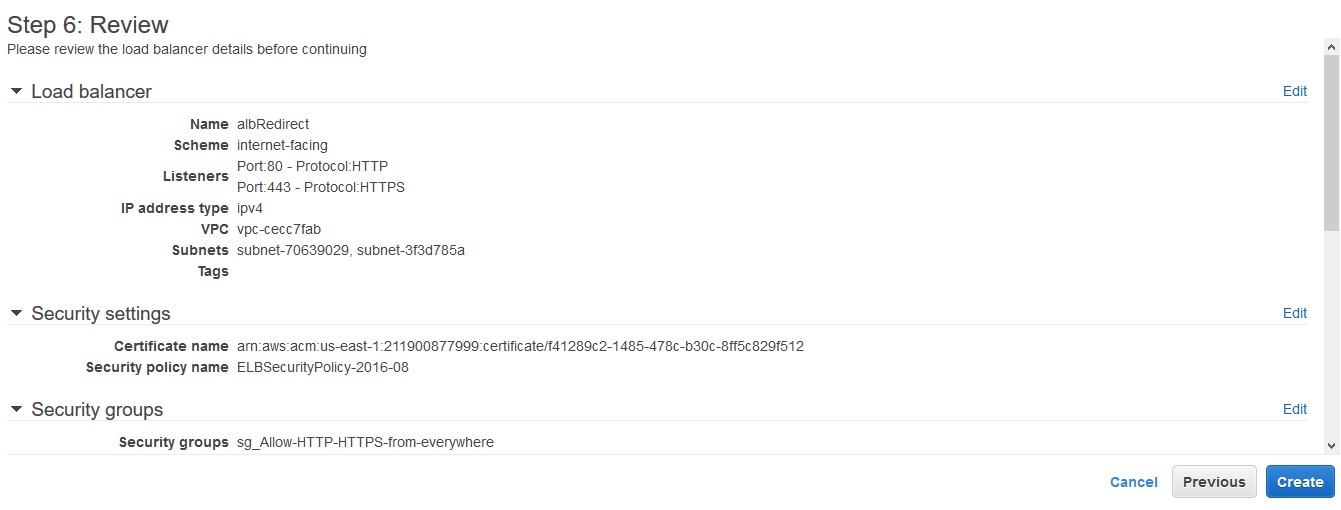
Click on Next: Register Targets. Even if you have your servers in AWS, it doesn’t matter. A target is necessary for an ALB, but we are not using that functionality. Just click Next: Review and if everything looks good, click Create under step 6.
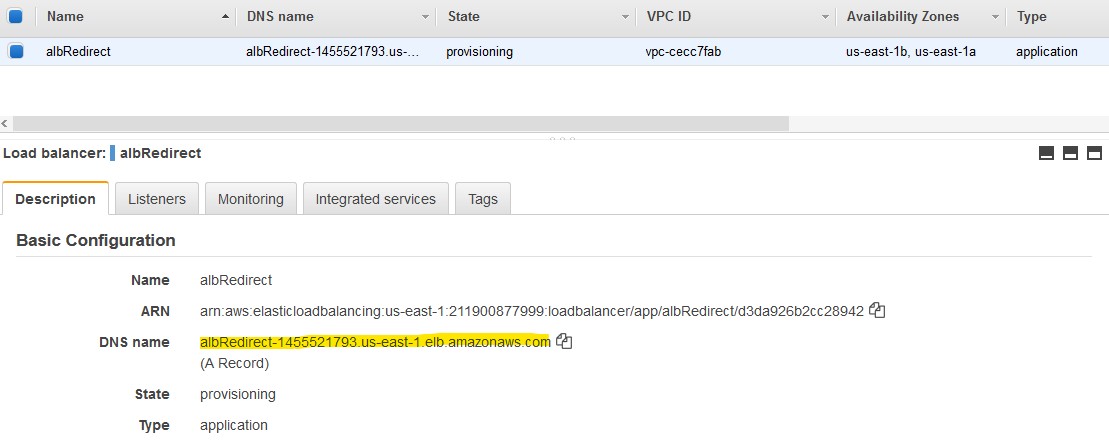
It takes about a minute or two to provision the load balancer. While it’s provisioning get the DNS name of the load balancer (under Description tab).
Rules
Click on the Listeners tab and then View/edit rules for port 80. You’ll see the Rules page.
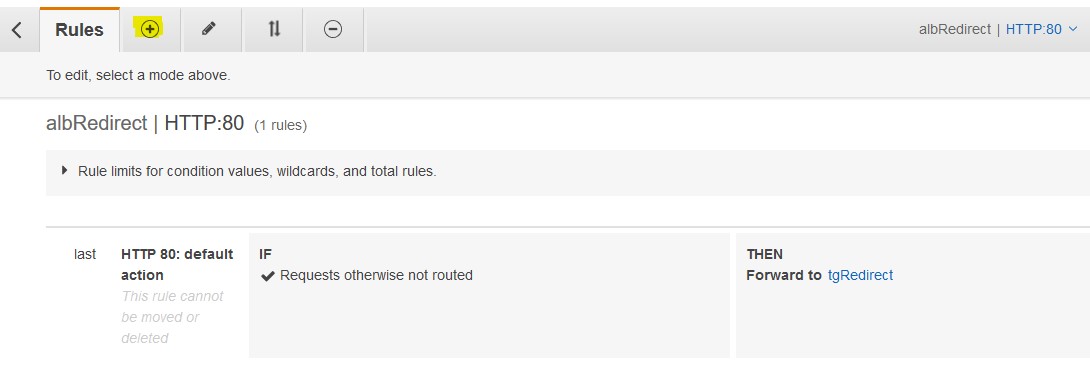
Click on the plus (+) sign to add a new rule then click on (+) Insert Rule. Click on (+) Add condition and then select Host header.
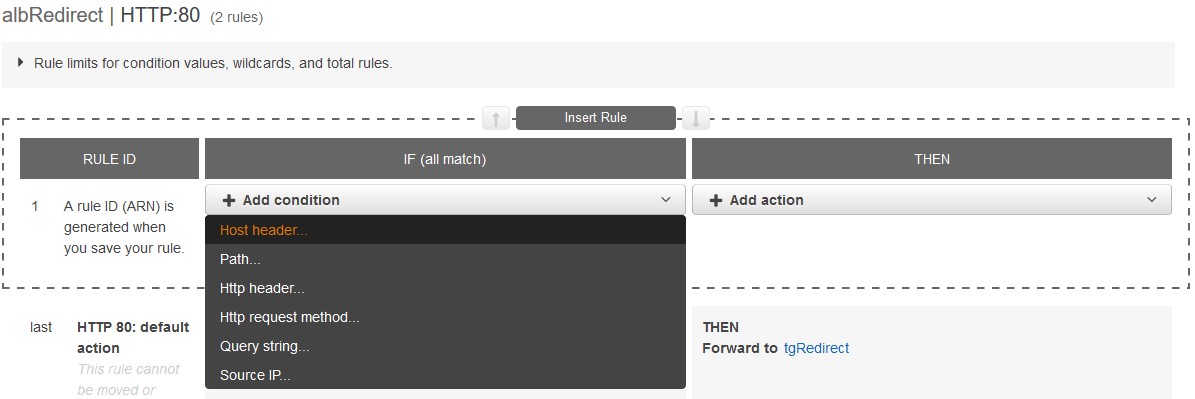
Enter the first source URL in my case legal.andreev.it. Then on the right, click (+) Add action and select Redirect to…I’ll redirect legal.andreev.it to https://www.futurebit.com/legal-andreev so my config looks like this.

Click Save in the upper right corner.
IMPORTANT: Do the same for port 443. In the upper right corner where it says albRedirect | HTTP:80 click on the down arrow and select port 443. Again, create the Host header rule and the Redirect rule. These should be the same for port 80 and 443. See screenshot above.
Before we test further, make sure that your destination URLs are working.

DNS
Go to the DNS of the source domain and add a CNAME record for legal.andreev.it to point to the load balancer’s DNS. This is what it looks like for my setup.

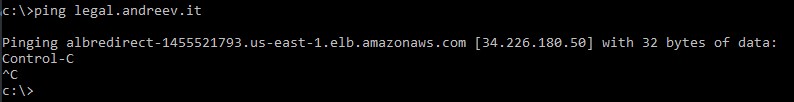
Make sure that your CNAME resolves. If the redirect doesn’t work, ping your source domain (in my case legal.andreev.it) first and see if it resolves. If it doesn’t – wait until the DNS replication is completed.
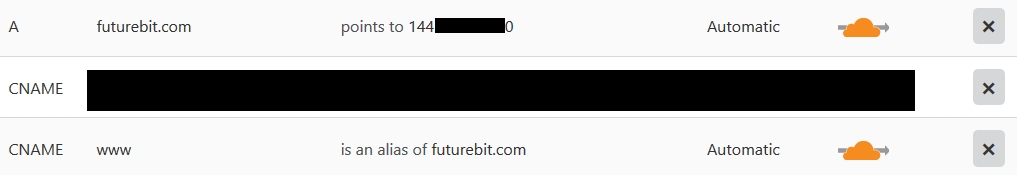
Once the replication is completed, the redirection should work. My destination domain is behind Cloudflare. This is the config in DNS.
I don’t have any page rules there. I do the redirect on Apache level. It really doesn’t matter where you do the redirects from HTTP to HTTPS. The only setting I have is under Crypto option in Cloudflare. The SSL is set to Full instead of Flexible which is the default. If you have too many redirects errors, this is probably the cause.
Add second certificate
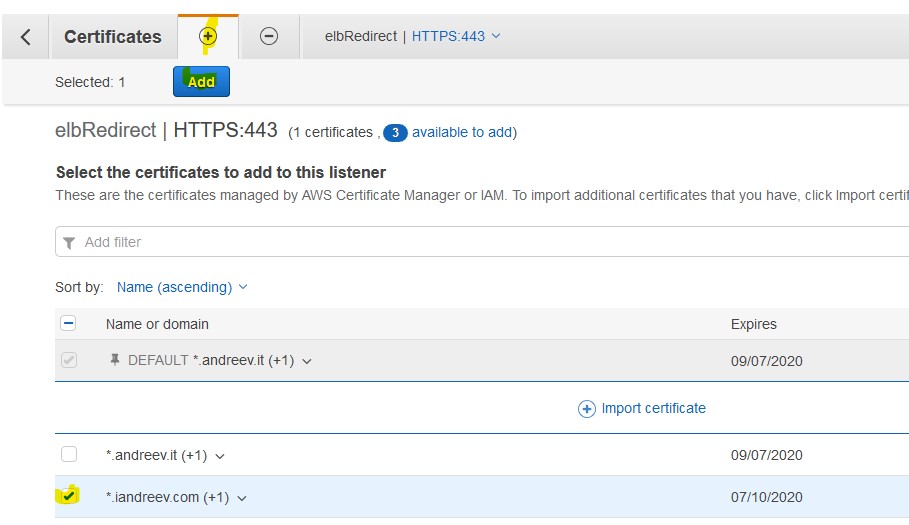
By now, you have one domain working. If you want to add the second domain, you have to attach a certificate to the ALB listener. Go to the ALB, click on the Listeners tab and click View/edit certificates. Click on the plus (+) sign and select a new certificate, then click Add. In my case, I just added the second certificate iandreev.com.
Now, if you want to add the second domain redirect, just go back to Rules and redo everything for the 2nd domain.

