I had a request for a full access to Glacier. I had to explain that full access is an overkill and that full access to a vault should be sufficient. So, the requester will have full access to his vault, but won’t be able to create, modify or delete any other vaults.
First, create the vault in Glacier. Enter the vault name, configure the SNS notifications if needed and click Submit.
Next, create the IAM user that will have the access to Glacier. Grant this user both Programmatic access and AWS Management Console access. Once you create the user, assign the user the following Inline policy.
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Resource": "arn:aws:glacier:us-west-2:<AWS_account_no>:vaults/vaultname",
"Action": [
"glacier:*"
]
},
{
"Action": [
"glacier:ListVaults"
],
"Effect": "Allow",
"Resource": "*"
}
]
}
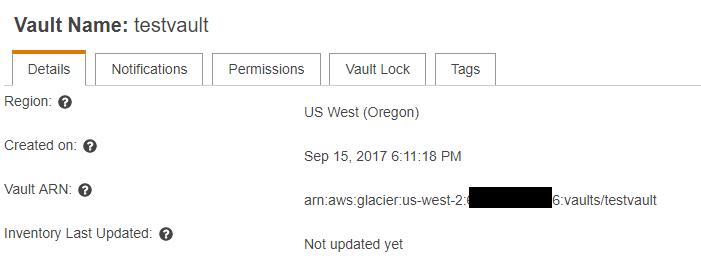
Make sure that you modify line #6. Replace with your region (e.g. us-west-2), AWS account (12-digit number) and the vaultname. You can get this ARN if you click on your vault and expand it.
Send the user the URL (https://AWS_account_no.signin.aws.amazon.com/console), his IAM username and password and the credentials.csv file so he/she can access it both from the console and from CLI/API.

